“Understanding and harnessing the persuasive powers of narratives is central to US and international counter-terrorism efforts. There is an urgent need to understand the narrative tactics of terrorist recruitment and equal if not greater need to destabilize the weakness of those narratives.” (Ajit Maan PhD, Narrative Strategies: Counter Terrorism http://www.ajitkaurmaan.com/books-and-articles.html)
Since 9/11 we have seen increasing sophistication in the use of narratives by al- Qaeda, its affiliates, and especially by Daesh, to shape the minds of their international audience. Well scripted secular narratives often illustrated by skilfully edited visual images drive home the message to young people that they are being oppressed by the western world- the west is inherently racist and all their experiences: lack of work and education opportunities, marginalization and all social problems, both real and imagined, are because of the corrupt western governments which is being supported by Christian-Jewish elitism.
Secular narratives are designed to create a culture of blame towards the western nations and those outside their peer group. Religious narratives, or to be more precise the extremist’s version of Islam, provide not only strong moral justification for violent Jihad but also provides a peer-group of like-minded individuals willing to use violence to address their perceived grievances. The occasional outbursts of resentment from an individual has been transformed into collective action to violently challenge the status quo.
Once an individual has been suitably spoon fed with the urgent need to act, violent Jihad is far easier to sell as a religious duty. The cognitive effects of the combination of secular and religious narratives closely fit Jerome Bruner’s (American psychologist) concept of ‘Narrative Construction of Reality.’ It may also be described as ‘Narrative Based Knowledge’ (Nicolas Szilas).
Although narrative analysis (narratology) can be complex, in principle we can break it down into Emotions, Motivation and the mobilization of Action.
An example of Daesh attempting to increase civil unrest in the USA and promoting the illusion of the Islamic State embracing equality among all races.
Narratology (the analysis of narratives in their many forms)
Since the 1960’s Narrative theorists have always shown interest in the relation between minds and narratives, or to put it another way, the cognitive effects of narratives. Although many argue that Narratology was starting to be regarded as an important area of research during the 1960s, throughout the 1960s and well into the 1990’s this research was being conducted by scholars from a wide variety of disciples which included: Social Anthropologists, Philosophers, Social Historians, Psychologists and Sociologists. Each disciplined tended to work in isolation resulting in their findings, the development of concepts and analytical tools not being shared with other disciplines and there were no peer-group reviews from outside their profession. I am pleased to see that Narrative Strategies (http://www.narrative-strategies.com/) has started to address this major shortcoming by establishing an increasingly influential public platform consisting of a coalition of scholars and military professionals involved in the non-kinetic aspects of counter-terrorism, irregular warfare, and social conflict.
When attempting to analyse narratives from Daesh and AQ affiliates we find ourselves attempting to identify how these various narratives are designed in order to “construct reality” for a specific audience. Only then is it possible to construct a workable counter narrative. Furthermore, an added difficulty is due to the fluidity of the narratives used by Daesh and AQ. These organisations closely monitor all government communications, the media and pay close attention to international affairs and western military initiatives. They look for every opportunity to distort the original message to fit their propaganda objectives.
A simple example which has been much quoted occurred shortly after 9/11 when George W. Bush said, “this crusade, this war on terrorism is going to take a while…” within hours the word ‘Crusade’ was used to project the image of America being the aggressor against Islam. They received a further propaganda opportunity after columnist Alexander Cockburn, suggested in the Counter Punch magazine, that Bush was referring to the “Tenth Crusade” in which he numbered America’s War on Terrorism to follow the nine medieval crusades between 1095 and 1272. As Bush used the word ‘crusade’ and an American publication ‘confirmed’ the USA was going to continue the medieval European crusade against Islam this was not only used as confirmation that America was bent on destroying Islam, 9/11 was also portrayed as being ordained by God! As can be seen by this example of one word resulting in a huge propaganda victory which was used for moral justification for terrorism, recruitment and proof that Jihad against America and its western allies was the duty of all Muslims, most government communications which lack close scrutiny may be used for propaganda purposes simply through careful manipulation based on cultural and social interpretations; and the distortion of the original message to support the extremist mythology based on their view of an unjust and un-Godly world in which the west continues to be responsible.
The current threat from international terrorism cannot be addressed by conventional and SOF alone and the use of soft power, for example, the ability to shape the preferences of others through appeal and attraction, are essential for countering this new terrorist phenomenon based on ideology and destruction.
I agree with Paul Cobaugh who says, “The US soft power tool box is half empty and poorly stocked… we are employing an ineffective, ambiguous, antiquated strategy and there is a limited number of true, trained craftsmen…”
(Paul Cobaugh, Soft Power on Hard Problems (forthcoming) ed. Ajit Maan, Ph.D. and Brig. (retired) Amar Cheema.)
I would add, this is not just a US problem, all western nations share the problems addressed by Paul Cobaugh. Again, I also agree with Paul Cobaugh’s assertion that “Daesh is a media influence effort supported by arms and brutality rather than the other way around” and “We require sophisticated media campaigns in the media and on the ground…”
Due to the powerful and fluid nature of the plethora of Daesh narratives I also agree with Paul Cobaugh’s view that those responsible for government or military communications must be capable of thinking out of the box and we must also utilize the media, diplomacy, business development etc. This multi-faceted approach which Paul Cobaugh discusses in great detail, are clearly essential for establishing workable and fluid counter narratives both inside theatres of operations and also to address secular and religious narratives which continue to be powerful recruiting tools especially when it comes to valuable men and women living in the west and also provides opportunities for the development of the ‘self-radicalized’ and so-called lone wolf attacks.
Furthermore, any efforts in the form of refugee aid and stability development, irrespective of whether this is a government or NGO initiative should be widely promoted. (See Ian Bradbury, Narrative Strategies http://www.narrative-strategies.com/) Humanitarian work of this nature helps counter the narratives depicting western nations being led by the epitome of evil (the United States) and the Christian- Jewish alliance to crush Islam.
The Digital Culture: Finding and analysing the continuous flow of Narratives.
Apart from analysing narratives with the intention of countering their message or story, such analysis may also provide information on the target audience, the writer and his/her intentions and this is especially true with western audiences. Of particular interest is language syntax- informal speech patterns, country or regional variations, jargon, teen idioms and expressions, Pidgin English etc. However, an increasing problem is finding the narratives to analyse in the first place.
It is well known that Twitter, Facebook and YouTube continue to be used by Daesh and AQ affiliates for the dissemination of propaganda and are also used for recruitment. It is also known that as soon as these accounts come to the attention of network monitors they are deleted but only to be replaced by large numbers of new accounts which are often linked to disposable email accounts. Furthermore, some accounts may deliberately use expressions which are not connected with extremism or religion in order to avoid detection and subsequent suspension of the account.
In 2013 I said, in ‘Narrative: Pathways to Domestic Radicalization and Martyrdom’, every effort is being made to recruit technical-jihadists and IT professionals specializing in security should not be complacent by believing they are the smartest people in their field. Some of my IT contacts remained adamant: they held graduate and post graduate degrees and had far greater knowledge and experience than any terrorists. Since then we have seen an increasing degree of cyber sophistication and media manipulation from Daesh technical jihadists.
Although Daesh continue to use multiple Twitter, You Tube and Facebook accounts and easily form new accounts to replace those which have been removed, these and other mainstream social media networks are now mainly used as conduits to steer willing audiences and potential recruits to more secure networks which us various forms of encryption and the choice of network is sometimes used to target a particular geographical area.
Blackberry Channel
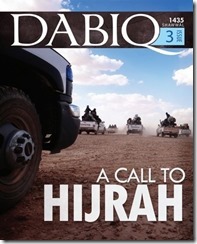
Blackberry’s media platform, ‘Channel’, according to IBRANO, have over 1 million channels which can only be accessed through Blackberry Messenger and users can start channels covering topics of their choice. The Al-Hayat media wing of Daesh, who publish the Dabiq Magazine, have been found using the Blackberry Channels. According to ARS Technica, Channel is used to target an English speaking audience and is regarded as a versatile recruiting tool which Daesh regards as far more effective and more secure than their estimated 46,000 Twitter accounts (ARS Technica).
In 2015, the BBC reported that “new platforms are popping up on a weekly basis in order to get away from mainstream social media platforms and to hide in corners…” (BBC Trending, 13 March 2015)
We now find that many of the narratives we need to address along with the planning of attacks, recruitment information, bomb making instructions; ideological literature, advise on how to engage in so-called lone wolf attacks against soft targets, and other instructional, motivational material and advice, is being sent to willing audiences and the fully radicalized via secure mobile messaging apps some of which have been designed by technical jihadists.
Telegram, which is described as a cloud-based instant messaging service for both mobile (Android, iOS, Windows Phone, Ubuntu Touch) and desktop systems (Windows, OS X, Linux) allow users to send messages and exchange photos, videos and files of any format up to 1.5 GB in size and has extensively been used by Daesh and AQ Yemen (AQAP). This was a natural choice simply because Telegram provides optional end-to-end encrypted messaging with self-destruct timers. According to promotional material it is “Pure instant messaging — simple, fast, secure and synced across all your devices and has over 100 million active users.”
For Daesh, Telegram provides two major security requirements. Firstly, it has been widely said Telegram does not disclose where it rents offices or which legal entities it uses to rent them, citing the need to shelter the team from unnecessary influence and protect users from governmental data requests. Secondly, it is also widely claimed that once the self-destruct timers have been activated and all data has been deleted no data can be recovered using forensic software. Naturally, both claims are open to debate.
Telegram and other encrypted apps are also used to distribute their publication ‘Inspire’ which concentrates on training and their glossy magazine Dabiq which has a strong media brand and is designed for the dissemination of ideological congruent propaganda to promote radicalization among sympathizers and foreign fighters mainly from the English speaking nations.
Daesh also maintain their electronic presence and distribute their narratives by adopting per-to-peer technology. For instance, anonymous peer-to-peer networks such as Ask.Fm was used for one-to-one interaction, and the distribution of information on how to join Daesh.
It is also known that Firechat app has been utilized for covert planning of coordinated attacks and also for international recruitment.
According to the Office of University Programs and Technology Directorate, US Department of Homeland Security, in December 2014, “After profiling this group’s {Daesh} use of cyber technology for over a year they found the use of a variety of technical platforms, diverse languages and tailored messages… cyber technologies also facilitate internal co-ordination (e.g. Command and control) and focused information flow externally with the broader Umma {the whole community of Muslims bound together by ties of religion} and potential foreign fighters.”
This paper also explains Daesh has a sophisticated understanding of cyber marketing, organisational branding and has robust and a fluid recruitment arm and highlights the kind of personal information they can access.
Apart from the intelligence and security implications associated with encrypted communications over several platforms it also presents a series of hurdles we must overcome before we can counter the stream of narratives from Daesh and the various AQ affiliates.
Daesh using race to promote the ‘virtue’ of their ideology.